A Comprehensive Guide to Smart Contract Auditing

Listen to the article
When the concept of smart contracts was first introduced in 1996 by Nick Szabo, it could not evolve beyond theory. It was confined to papers until the development of blockchain technology. However, the first blockchain, namely Bitcoin, does not support smart contracts natively; the blockchain protocols that were developed later introduced this concept.
When Ethereum came into existence in 2015, it made smart contracts a reality, and the use of smart contracts has been extensive ever since. Currently, smart contracts power many applications, including financial applications, real estate, supply chain, healthcare and more.
With this steady growth of smart contract usage, the need to make more secure, reliable and bug-free smart contracts increased so that no one can tamper with the applications they back. As such, smart contract audit has become a mandatory step in smart contract development. A smart contract audit is a process of reviewing the codes of a contract to ensure that it is reliable, efficient and secure. The purpose of the audit is to leave no loopholes or vulnerabilities that any bad actor can misuse. A smart contract audit is undertaken by experts with extensive knowledge of smart contracts and blockchain technology to ensure there is no loophole in a smart contract’s codes.
Through this article, let us go in-depth about the significance of smart contract audits and their various aspects.
- What is a smart contract?
- Smart contract vulnerabilities
- What is a smart contract audit?
- Why is a smart contract audit necessary?
- Types of smart contract audit
- The smart contract auditing process
- What smart contract vulnerabilities does a smart contract audit address?
- Classification of audits’ findings
- Audit findings difficulty/likelihood
- Important audit techniques
- What technologies does LeewayHertz use to audit smart contracts?
What is a smart contract?
Smart contracts are self-executing contracts wherein the terms of an agreement are written directly into lines of code, which are then stored and replicated on a blockchain network. No third-party intervention is required to initiate the code and the agreement between the buyer and seller; they execute by themselves when the parties involved reaches a consensus. By automating the execution and enforcement of contracts, smart contracts lower the risk of errors, fraud and miscommunication. They can be used to facilitate, validate, and carry out the negotiation or performance of a contract.
Smart contract vulnerabilities
Smart contracts are exploitable and prone to hacking when neglected. The Decentralized Autonomous Organization (DAO), launched on the Ethereum blockchain in 2016, is a prime example of smart contract vulnerability. The DAO was a smart contract intended to be a decentralized investment fund that amassed over $150 million from more than 11,000 investors during its Initial Coin Offering (ICO).
However, owing to a security loophole in the codebase of the contract, a hacker exploited the vulnerability to seize nearly one-third of the funds from the DAO. This led to a loss of over $50 million in funds, which eventually resulted in a hard fork of the Ethereum network to retrieve the stolen funds. Because the project was heavily invested on, its smart contracts held approximately 14% of the collected Ether (ETH) in circulation. As a result, the budding Ethereum technology faced a serious existential threat.
The goal of a smart contract audit is to avoid such situations. If the smart contracts of the project had been properly audited, the incident would not have occurred. Instead, the exploitable codes and their weaknesses would have likely been identified and addressed in a smart contract audit, preventing the incident from occurring.
What is a smart contract audit?
A smart contract audit is a process of carefully scrutinizing the codes of a smart contract before deploying it. As smart contracts are immutable, they cannot be edited after deployment. As such, they have to be thoroughly examined to find the possibilities of any bugs and vulnerabilities so that they may not affect the functionality of the project once deployed. Smart contract audits are, thus, conducted to optimize codes and enhance their integrity.
During a smart contract audit process, developers inspect the source code of the contract line-by-line to identify if the code has any security loopholes or vulnerabilities. After the identification, the lines of codes with faults are rectified and fixed. This can reduce the code’s potential risks and improve the code’s quality.
Why is a smart contract audit necessary?
As smart contracts handle valuable assets worth millions, ensuring they are free of vulnerabilities is imperative to leave no room for attackers to manipulate the assets. A smart contract audit can help mitigate security risks associated with the contract’s code and is vital to the project’s life cycle. It is beneficial for a project in the following ways:
-
Increased security – Performing a smart contract audit helps identify possible security vulnerabilities and other risks associated with the contract’s code. Developers can then work on the discovered issues to fix them and strengthen the security of the smart contract so that the project remains tamper-proof and protected against malicious attacks.
-
Improved optimization – Conducting a smart contract audit service can optimize the contract’s source code by exposing any indirect command execution like runtime error, reentrancy, interface issues, unknown code, gas-intensive operations and other flaws.
-
Better functionality – Auditing a smart contract can ensure that the contract functions as intended. It can verify if the contract meets the specific requirements and purposes of the project or institution and examine if the contract has deviated from the project’s original goal.
-
Compliance and regulatory approval – Organizations that require compliance with industry-specific or governmental requirements can benefit from smart contract audits to ensure their contracts adhere to relevant standards and regulations.
-
Boosts performance – Auditing a smart contract before deploying it can streamline its automation process. It helps to trigger the smart contract without hindrances or glitches and helps boost its overall functionality.
-
Higher efficiency – Audits are beneficial in improving the efficiency of your code by confirming if it is well-written and organized while also validating that all associated variables and functions go according to the project’s intended purpose and goal.
-
Enhanced user trust – A smart contract audit builds trust with users, demonstrating that the contract has been thoroughly examined and any issues have been resolved.
Types of smart contract audit
Depending upon the nature/status/scope of a project, smart contract audits can be categorized into the following:
New audit
A new audit is performed when a smart contract is created for a project that is about to launch. The key objective of this audit is to find and fix any potential flaws or defects before the contract code is implemented on the blockchain. It is also known as a pre-deployment audit and includes a security audit, functional audit, compliance audit, and code review.
Repeat audit
A repeat audit occurs when a new version of an existing project is created. Its main objective is to review new additions, modifications, or adjustments to a smart contract. It aims to ensure that the modifications made to the contract do not create any new security flaws or have a detrimental influence on its general performance. This audit usually comprises a code review, security, and functional audit.
Fix audit
This kind of audit is conducted following the identification and correction of flaws by the development team and is targeted at ensuring that the smart contract’s patches solve the issues that were found and do not create any new vulnerabilities. A fixed audit is carried out whenever a smart contract is updated.
Retainer audit
A retainer audit is carried out regularly on an ongoing basis, with a team or organization keeping an auditor on retainer to examine and evaluate the smart contract regularly. This helps evaluate the smart contract’s security regularly and to swiftly find and address any problems that may develop.
Incident audit
An incident audit is executed when an exploit or security incident has been discovered in a smart contract. The core objective of this audit is to identify the genesis of the incident, evaluate the underlying vulnerabilities and suggest fixes to restrict similar occurrences in the future.
Hire LeewayHertz’s smart contract audit service
Protect your dApps and blockchains from security breaches with fully audited smart contracts
The smart contract auditing process
To conduct a proper smart contract audit, the firm should follow certain norms and techniques in a structured manner. Although the structure of the auditing process can vary from company to company, the overall outline remains the same in general. Let us go through each step of a generic smart contract auditing process.
Specification gathering and client consultation
A smart contract audit can only occur with a deep understanding of the project’s details. So, the first step of auditing a smart contract involves studying the project by consulting the client and gathering specifications. In this step, an auditor comprehends the framing of the code, its design, architecture, build process and other vital information to understand the intended behavior of the smart contract.
Automated review and testing
In this step, an auditor leverages sophisticated and high-end tools and software, like Quill Hash, Slither, Certik’s SkyHarbor and more, to review and analyze the contract codes. This step inspects the source code to identify if it has any potential risks like security loopholes, bugs, syntax errors and exploitable and weak codes.
Manual analysis and testing
Errors and code loopholes missed in the automated review and testing are caught in the manual analysis and testing phase. Here, the auditors examine the code line-by-line to find whether the smart contract presents any unanticipated behavior or security vulnerabilities like reentrance, denial of service, overflows, time manipulation, front running, logical flaws and malicious libraries.
Functional Testing
In functional testing, each function and method is tested on multiple parameters and conditions for any error and confirm if each contract function performs as outlined in the specifications. In this phase, the auditor verifies and ensures that the smart contract does not deviate from its intended behavior. It also involves checking if the smart contract executes any gas-intensive operations and testing if the operational and business logic are implemented properly.
Initial audit report submission
Once the smart contract is thoroughly inspected for any vulnerability, the team of auditors of the smart contract audit company submits an initial audit report. This audit states all the findings and effective recommendations to fix or rectify the issues.
Rectifying the codes
After submitting the initial audit report, developers fix the issues and bugs detected based on the suggestions mentioned in the initial report. The codes can be rectified from either the client side or the audit firm, as per the client’s requirement.
Inspecting the fixed codes
Once developers fix the codes, the audit firm again reviews the rectified smart contract and runs a series of tests to authenticate if the code quality has improved and all loopholes have been addressed.
Final report documentation and submission
This is the final step in a smart contract auditing process. It involves documenting each detail and critical information of the smart contract auditing process to hand over a transparent, fully customized and comprehensive report to the client. A smart contract audit report details differ from company to company. However, generally, a smart contract audit report involves the following:
-
The goal of the project
-
The effort
-
Audit approach
-
Audit techniques
-
Audit tools
-
Detected vulnerabilities and their severity
-
Summary of the findings
-
Recommended remediations
-
Vulnerability fixes
-
Time duration
What smart contract vulnerabilities does a smart contract audit address?
There are several issues common to smart contracts that can be detected through an audit, including the following:
-
Reentry attacks – This happens when a threat actor repeatedly calls a function in a smart contract, enabling them to drain the balance of the contract or conduct other malicious deeds. In smart contract audits, reentry vulnerabilities can be detected by looking for instances where external actors repeatedly call specific functions in the contract.
-
Syntax errors – Syntax errors can hinder the functioning of smart contracts, preventing them from operating as intended and increasing security risks. By performing a smart contract audit, you can identify such errors in the code, which are frequently caused by logical or structural mistakes.
-
Frontrunning – This attack occurs when a bad actor can see and act on transactions before they are confirmed on the blockchain by assuming their timing and order. It is possible to prevent this by auditing smart contracts to identify ways malicious actors might gain an informational advantage over other actors in the contract.
-
Undefined behavior – During smart contract audits, undefined behavior can be detected by locating areas in the code where the behavior of the contract is unclear, creating confusion and vulnerabilities.
-
Integer overflow and underflow – It is one of the most common errors found in smart contract development, wherein a contract tries to execute a mathematical operation that exceeds the maximum or minimum number that can be represented by the data type used. Smart contract auditing can overcome this issue using a formal verification technique.
-
Data exposure – During smart contract audits, variables, memory locations, and external calls that leak sensitive information to the public can be identified.
-
Timestamp dependence – Malicious actors can manipulate a smart contract that relies on the current timestamp for important decisions. By identifying parts of the code where timestamp dependence affects the contract’s behavior, auditors can detect timestamp dependence.
-
Denial of service (DoS) attacks – In a DoS attack, a hacker overloads the contract by using many transactions or requests and prevents the contract from functioning properly. During an audit, areas of the code prone to high traffic or other forms of overload can be detected and resolved.
Classification of audits’ findings
The vulnerabilities detected in the code during a smart contract audit are often divided into distinct categories to understand their nature, potential consequences, and exploitability. Developers can prioritize the issues according to their classification, providing information on the severity of vulnerabilities, which project functionalities or components are impacted, and potential scenarios for their exploitation.
Depending on the audit service provider or tool, the classification of the identified vulnerabilities may change. As a smart contract audit company, LeewayHertz utilizes the following categorization system:
-
Access controls: These flaws concern user authentication and evaluating their rights within the smart contract. Examples include insufficient role-based access controls or improper authorization checks for critical functions.
-
Auditing and logging: These issues concern the auditing of smart contract actions or logging errors as they happen. This covers problems like inadequate event tracking or flawed auditing of crucial actions.
-
Authentication: It involves concerns with weak or easily hackable authentication processes pertaining to identifying users within the smart contract.
-
Configuration: These flaws involve the smart contract’s security configurations, such as problems with hardcoded private keys or unsafe default settings.
-
Cryptography: It is related to safeguarding the confidentiality or integrity of data stored or processed by the smart contract and includes problems with insufficient encryption or a lack of appropriate cryptographic controls.
-
Data exposure: These flaws relate to unintentional disclosure of private data, such as data leakage via events, debug/logging information or state variables.
-
Data validation: These flaws are related to the unintentional exposure of sensitive data to the public.
-
Denial of service: These flaws involve the possibility of creating system failure, such as infinite loops.
-
Error reporting: These flaws are related to the secure reporting of error conditions, such as problems with unhandled exceptions, panics, or reverts.
-
Patching: It involves flaws related to keeping software up-to-date, like problems with outdated dependencies and unapplied security updates.
-
Session management: These flaws, such as problems with session fixation, session hijacking, or improper session invalidation, affect the identification of authenticated users.
-
Timing: These weaknesses include locking, racing conditions, or the sequence of events.
-
Undefined Behavior: These issues relate to the contract’s undefined behavior, such as internal inconsistency checks or interactions with other contracts.
Hire LeewayHertz’s smart contract audit service
Protect your dApps and blockchains from security breaches with fully audited smart contracts
Important audit techniques
Audit techniques are a collection of methods applied to a codebase and its accompanying documentation and specifications. These techniques involve automated analyses performed using tools and manual assessments.
Manual techniques
Manual techniques are the most time-consuming and resource-intensive, requiring thorough human input. Manual techniques include the following:
Specification analysis
Specification analysis is the process of reviewing the specifications or detailed documentation that sketches the functional design and architecture of the project. This documentation elaborates on the project details, including what the project and its components are intended to do and why they are supposed to perform in a particular way. From a security perspective, a specification provides important information about the assets of the project, where they are located, who the actors are, the privileges of these actors, who are authorized to access what and when, the trust relationships between different components, the threat model, potential attack vectors, scenarios, and mitigations.
Conducting a specification analysis allows auditors to evaluate the assumptions made during the design and development of the project and identify any shortcomings. This can help them understand the security controls in place and focus their vulnerability assessment efforts on specific areas of concern.
Documentation analysis
Documentation analysis is reviewing the written materials that describe how a project has been designed, architected, and implemented based on the design and architectural requirements. These written materials, known as documentation, provide insight into the ‘how’ something has been implemented/architected but not necessarily the ‘why’ and the design/requirement goals. Typically provided as the readme files, documentation outlines the functionality of individual contracts, along with functional NatSpec (Natural Language Specification) and individual code comments. Several times, documentation acts as a substitute for specification, offering vital information about the project team’s goals, requirements and assumptions.
Performing a documentation analysis allows auditors to comprehend the project’s architecture, the interactions between contracts, asset flow, program constraints, threat model, actors and risk mitigation measures, which can help them save time when deducing this information from the codebase. Also, mismatches between the documentation and the codebase can hint at issues such as poor documentation, software defects or security vulnerabilities.
Automated techniques
Automated techniques involve using tools and software to audit the smart contract. The methods that fall under this category include:
Testing
Smart contract testing is similar to software development testing, where developers check if the contract behaves as intended but is comparatively more complicated despite its relatively smaller size in terms of lines of code. One of the reasons is that smart contract development platforms (such as Truffle, Embark, Brownie, Waffle, and Hardhat) are relatively new and have varying levels of support for testing. Additionally, smart contract projects generally need more testing done at the audit stage. Test coverage and test cases are good indicators of project maturity and provide valuable insights to auditors into assumptions and edge cases for vulnerability assessments.
Static analysis
Static analysis is a technique for evaluating the properties of a program without executing it. This method contrasts software testing, where programs are run with different inputs to observe their behavior. Various tools can be used to perform static analysis, such as Slither, which analyzes the Solidity code, and Mythril, which analyzes EVM bytecode.
Static analysis typically employs a combination of control flow and data flow analysis. Control flow analysis inspects control flow through the program and can identify issues such as missing return statements, infinite loops or other control flow issues. Data flow analysis evaluates the flow of data throughout the program, including how data is stored, used, and reorganized. This can help identify race conditions, data leaks, or other data flow-related concerns.
Fuzzing
Fuzzing, or fuzz testing, automatically tests contracts by feeding them random, unexpected, or invalid inputs. The fuzzing aims to find any weaknesses or vulnerabilities in the contract, such as crashes, memory leaks, or failed built-in code assertions.
Fuzzing is particularly useful when testing smart contracts, where transactions can contain arbitrary inputs that the contract may not be prepared to handle. This can result in unexpected behavior and possible security vulnerabilities, making fuzz testing a critical tool for identifying and addressing these issues.
Formal verification
Formal verification involves using mathematical methods to prove or disprove the correctness of a system’s underlying algorithms about a specific set of properties or specifications. Formal verification can be especially effective at identifying complex bugs that may be difficult to detect through manual testing or simpler automated tools. By using formal methods to define the desired properties of a contract accurately and then mathematically checking that the incorporation of the contract satisfies these properties, formal verification can provide a high degree of assurance that the contract is functioning as intended, even during malicious attacks.
To perform formal verification, one first needs a precise specification of the program or system is verified, which defines the expected behavior and properties. Additionally, one needs techniques to translate or compare this specification with the actual implementation of the system.
Manual analysis
Manual analysis is a complementary method of evaluating smart contract security, often used alongside automated analysis tools. While automated analysis tools can be quick, inexpensive, and scalable, they are limited in the properties they can detect, typically focused on Solidity and EVM-specific constraints.
On the other hand, manual analysis involves human experts manually reviewing and evaluating the code and is typically more expensive, slower, and less scalable due to the rare and costly expertise needed. It has the advantage of figuring out and evaluating business logic and application-level constraints, where a significant number of serious vulnerabilities are typically found. Automated tools often don’t cover these issues, making manual analysis a crucial method in smart contract audits.
These techniques can be further classified into manual/semi-automated/fully automated. Fully automated tools are simple and require a little configuration but may not catch everything. Semi-automated tools tend to require more human assistance and are more resource-intensive, while manual analysis is the most resource-intensive but also the most thorough.
What technologies does LeewayHertz use to audit smart contracts?
LeewayHertz utilizes an array of tools and software to audit smart contracts, out of which the prominent tools include:
MythX
MythX is a security analysis platform for Ethereum smart contracts. Utilizing a combination of dynamic analysis, static analysis and symbolic execution, it identifies the possible vulnerabilities in smart contracts. The platform supports multiple smart contract languages like Vyper and solidity and can be accessed via numerous ways, including a Python API, a command-line interface (CLI) and several integrations with development environments such as Remix and Truffle.
SkyHarbor
A security analysis platform launched by Certik, SkyHarbor combines formal verification and manual testing to discover potential vulnerabilities in smart contracts. Utilizing formal verification, SkyHarbor rigorously proves the correctness of smart contracts. It confirms that the smart contracts behave according to the specifications, even in edge cases or during malicious attacks. SkyHarbor secures smart contract integrity and makes it robust by helping developers find and fix their contracts’ weaknesses.
QuillHash
QuillHash is a smart contract audit tool that leverages manual code review, automated testing and security best practices to evaluate and find risks in smart contracts. LeewayHertz utilizes the automated techniques of QuillHash to identify issues in the smart contract codebase. QuillHash can also be integrated with prominent testing networks like OpenZeppelin and Truffle to conduct smart contract testing and examine the results.
Conclusion
Smart contract auditing is vital to ensure the security, reliability and integrity of smart contracts before they are deployed to a live network. It involves thoroughly inspecting the contract’s source code by expert auditors and automated tools to discover and analyze the exploitable codes that bad actors can manipulate. It prevents malicious threats, data leakage, draining of funds locked in contracts and much more by identifying, evaluating and fixing the vulnerable codes and building people’s confidence in the contract and the associated platform. Further, conducting a smart contract audit reinforces the significance of preventing security risks rather than regretting them later.
Don’t let vulnerabilities compromise the functionality of your smart contract; get a professional audit today. Work with the LeewayHertz team of smart contract auditors to ensure the success of your smart contract!
Listen to the article
Start a conversation by filling the form
All information will be kept confidential.
Insights
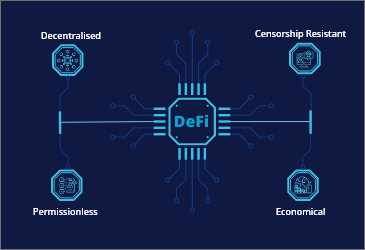
DeFi asset tokenization: Unlocking new possibilities
DeFi asset tokenization is the next step in the evolution of securitization, made possible by blockchain technology.
Wrapped tokens: An innovative approach to interoperability
Learn how wrapped tokens play a critical role in enabling cross-chain interoperability and in providing new financial services within the blockchain ecosystem.
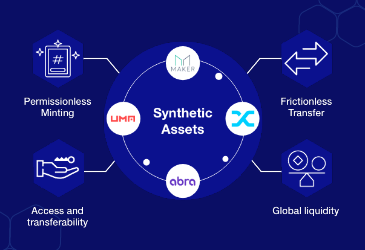
What are synthetic assets in decentralized finance
Crypto synthetic assets are gaining popularity in the crypto world as they allow investors to benefit from token fluctuations without actually owning them.